16 Mar
I go through about 25 cybersecurity news portals and blogs every week and pull out the most interesting stories. Then I turn them into this short, digestible summary, so you can stay up to date without trying to follow 25 different sources yourself. 😱
My aim is to create a summary that gives you the gist without needing to open up the source article. But if you do want to dig deeper, all the sources covering the event are linked below each story.
If you enjoy these, come back next Monday
scroll to the bottom to subscribe to the e-mail newsletter.
1. Ongoing GitHub account takeovers inject identical Python malware via force-push across hundreds of repositories
StepSecurity reports an active campaign compromising hundreds of GitHub developer accounts and silently injecting the same obfuscated malware into hundreds of Python repositories by rebasing the latest legitimate commit and force-pushing it to the default branch.The technique preserves the original commit message/author, making the change easy to miss while triggering malware when users run code or install directly from GitHub (e.g., `pip install` from a repo).The malware uses the Solana blockchain as command-and-control (C2) to fetch an additional encrypted payload, increasing resilience and complicating takedown efforts.
Key Details
- Earliest observed injections date to 2026-03-08; StepSecurity says new repos are still being compromised.
- Attack appends obfuscated code to common Python entry points such as `setup.py`, `main.py`, and `app.py`.
- Account takeover is tied to GlassWorm malware delivered via malicious VS Code and Cursor extensions;
- Stealth comes from preserving commit message/author/author date; only the committer date (and often committer email set to “null”) reveals tampering.
- While the final JavaScript payload cannot be analysed (it is AES-encrypted with a key delivered via HTTP headers), the infrastructure pattern is consistent with known crypto wallet stealer / infostealer campaigns
Next Steps
- Audit GitHub-installed dependencies for force-push tampering.
- Search your repos for `lzcdrtfxyqiplpd` indicator.
- Rotate GitHub tokens;
- Review VS Code/Cursor extensions.
Read more at StepSecurity
2. GlassWorm supply-chain campaign used 72 malicious Open VSX extensions and transitive dependencies to infect developer environments
Researchers reported a new GlassWorm campaign iteration that spreads through the Open VSX extension registry by abusing VS Code’s transitive installation behavior. Instead of shipping the loader inside an extension at publish time, attackers can publish a benign-looking extension first and later update it to pull a separate malicious GlassWorm-linked extension via extension relationships—reducing the chance of early detection.
Key Details
- Socket reported finding at least 72 additional malicious Open VSX extensions since January 31, 2026; the report was published Friday (referenced as March 13, 2026 by CybersecurityNews).
- The technique abuses the Open VSX/VS Code manifest fields “extensionPack” and “extensionDependencies” to trigger automatic installation of listed extensions.
- The malicious extensions impersonated common developer utilities (linters/formatters, code runners) and AI-coding assistant tooling (e.g., “Clade Code” and “Google Antigravity”).
- Socket noted GlassWorm behavior includes checks to avoid systems with a Russian locale and use of Solana transactions as a “dead drop” resolver to obtain C2 infrastructure.
- Aikido reported related Unicode-based malicious injections affecting an estimated 151 GitHub repositories between March 3 and March 9, 2026, and identified two npm packages using the same technique: @aifabrix/miso-client and @iflow-mcp/watercrawl-watercrawl-mcp.
- Examples of Open VSX extensions listed as removed include: angular-studio.ng-angular-extension, crotoapp.vscode-xml-extension, gvotcha.claude-code-extension, mswincx.antigravity-cockpit, tamokill12.foundry-pdf-extension, turbobase.sql-turbo-tool, vce-brendan-studio-eich.js-debuger-vscode.
Next Steps
- Audit VS Code extension dependencies.
- Block or tightly allowlist Open VSX extension sources.
- Monitor extension updates.
- Uninstall malicious extensions (full list available at Socket.io)
Read more at Socket.io, The Hacker News, CybersecurityNews
3. AppsFlyer Web SDK briefly served malicious JavaScript that swaps cryptocurrency wallet addresses
AppsFlyer confirmed its Web SDK temporarily delivered unauthorized JavaScript after a domain registrar incident, enabling a supply-chain attack against websites that loaded the SDK.The injected code could detect cryptocurrency wallet addresses entered on pages and replace them with attacker-controlled addresses to divert funds, while also exfiltrating the original address and related metadata.AppsFlyer’s SDK is widely embedded for marketing analytics, their website boasting about 15000 customers. So a single compromise can impact many downstream sites and end users even if the affected organizations themselves were not breached.
Key Details
- Malicious payload was served from the official domain: websdk.appsflyer.com
- AppsFlyer says the mobile SDK was not affected
- Profero observed obfuscated attacker-controlled JavaScript that preserved normal SDK behavior while hooking browser network requests
- AppsFlyer stated it found no evidence customer data on AppsFlyer systems was accessed
Next Steps
- Double check wallet addresses on multiple devices for crypto transfers.
- Don’t use your crypto wallets with your day-to-day browser and extensions.
- Audit JavaScript snippets on your website, and remove redunant or unneeded snippets.
Read more at BleepingComputer
4. Salesforce warns attackers are mass-scanning Experience Cloud sites for overly permissive guest user access
Salesforce is warning customers about active attacks targeting Experience Cloud sites—the public-facing portals companies use for customer communities, partner access, and help centers. Every Experience Cloud site has a guest user profile that controls what unauthenticated visitors can access. Attackers are mass-scanning these sites for instances where the guest profile has been left with overly broad permissions, then using a modified version of Mandiant's open-source AuraInspector tool to query CRM objects (contacts, accounts, cases) directly through the Aura API—even objects not visually exposed on the site.Salesforce says this is not a platform vulnerability but a customer configuration issue: admins often don't realize the guest user can query any object it has permissions on, not just what's displayed on the page.
Key Details
- Salesforce said the actor is using a modified AuraInspector tool to scan public-facing sites and extract data from instances with a guest user profile.
- ShinyHunters claims roughly 100 impacted companies; separately, screenshots cited by The Hacker News report a claim of “several hundred.”
- Salesforce characterized this as the third widespread attack spree affecting Salesforce customers in about six months.
Next Steps
- Audit Experience Cloud guest user permissions.
- Set Default External Access for objects to Private.
- Disable guest access to public APIs where possible.
Read more at CSO Online, CyberScoop, The Hacker News, BleepingComputer, The Register, Dark Reading
5. Storm-2561 uses SEO poisoning and fake VPN installers to steal VPN credentials
Microsoft reported a credential-theft campaign in which Storm-2561 manipulates search results to lure users to spoofed enterprise VPN download sites and malicious ZIP/MSI installers.The trojanized, digitally signed “VPN client” harvests VPN credentials via a fake sign-in prompt and exfiltrates them using a Hyrax infostealer variant, then attempts to reduce suspicion by showing an error and redirecting victims to legitimate vendor sites.
Key Details
- Impersonated/targeted vendors mentioned include Ivanti (Pulse Secure), Cisco, Fortinet, SonicWall, Sophos, Check Point, and WatchGuard.
- Attack flow includes SEO-poisoned queries (e.g., “Pulse VPN download”) leading to attacker-controlled sites and GitHub-hosted ZIP files containing MSI installers (repositories were later taken down).
- BleepingComputer reports the fake installer drops Pulse.exe under %CommonFiles%\Pulse Secure and side-loads dwmapi.dll (loader) plus inspector.dll (Hyrax infostealer variant).
- The malware establishes persistence using the Windows RunOnce registry key.
- Microsoft stated the malicious components were digitally signed using a certificate from “Taiyuan Lihua Near Information Technology Co., Ltd.” and that the certificate was revoked.
Next Steps
- Enforce MFA on everything.
- Provide vetted links to download approved corporate software like VPNs, messaging apps etc.
Read more at Microsoft Security Blog, BleepingComputer, The Hacker News, CSO Online
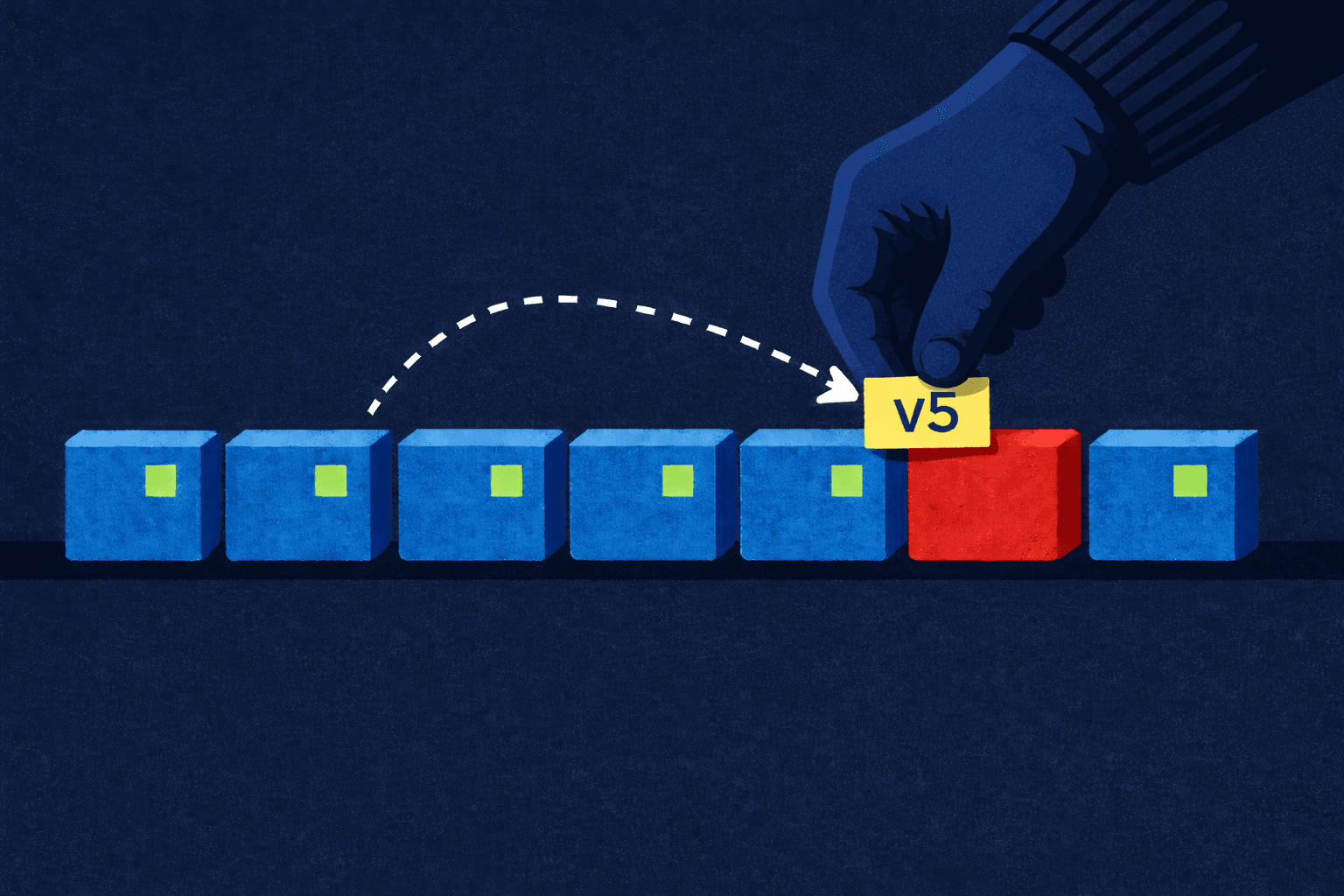
6. Xygeni GitHub Action compromised after attacker moved mutable v5 tag to malicious commit
Xygeni, which sells a number of AI-powered AppSec products, disclosed that its official GitHub Action repository (xygeni/xygeni-action) was compromised via “tag poisoning,” where an attacker moved the mutable v5 tag to a malicious commit after pull-request attempts were blocked by branch protections.Most teams treat version tags like fixed releases — pin to @v5 and trust it stays the same — but Git tags are mutable pointers that anyone with write access can silently move to a different commit. For roughly a week, any workflow referencing @v5 — across 137+ repositories — silently pulled and executed a C2 reverse shell instead of the legitimate scanner. The malicious code never reached main, but it didn't need to: the tag redirect was enough to distribute it to every downstream pipeline.
Key Details
- Initial malicious-code insertion attempts via pull requests were blocked by existing branch detection rules
- The attacker gained access via compromised credentials associated with a maintainer token with unnecessarily broad permissions.
- For roughly a week, any workflow referencing @v5 — across 137+ repositories — silently pulled and executed a C2 reverse shell instead of the legitimate scanner.
Next Steps
- Pin workflows to a known-good commit SHA.
- Audit CI logs for runs during exposure window.
- Rotate CI runner secrets potentially exposed.
- Update secure coding policies to require pinning to known-commit SHA-s not tags.
Read more at Dark Reading
7. Meta to end Instagram end-to-end encrypted DMs on May 8, 2026
Meta says Instagram will stop supporting end-to-end encrypted (E2EE) direct messages after May 8, 2026, and affected users are being told to download any messages and media they want to keep. The change reverses Meta’s multi-year push toward encrypted private messaging and means Instagram DMs will no longer have the strongest protection against platform access to message content.
Key Details
- Meta spokesperson cited low adoption: “Very few people were opting in to end-to-end encrypted messaging in DMs.”
- Meta has not clarified what happens to existing encrypted chats after May 8, 2026 (e.g., whether they are deleted).
- Meta directed privacy-focused users to WhatsApp (E2EE by default); Messenger retains E2EE for one-on-one personal chats, not for group or business communications.
Next Steps
- Update policies: prohibit sensitive data in Instagram DMs
- Notify users to export encrypted chats pre-May 8
- Shift to approved E2EE tools (e.g., WhatsApp)
Read more at The Hacker News, Cybersecurity News, Proton
8. US and Europol disrupt SocksEscort residential proxy network powered by AVRecon-infected routers
U.S. and European law enforcement disrupted SocksEscort, a malicious residential proxy service that sold access to malware-infected home and small-business routers so criminals could hide their true locations while committing fraud and account takeovers.Authorities say the service advertised access to hundreds of thousands of IP addresses globally and generated millions in revenue.
Key Details
- DOJ: From 2020–2026, SocksEscort offered access to ~369,000 IPs across 163 countries; ~8,000 were listed for sale as of February 2026, including ~2,500 in the U.S.
- Operation Lightning: 34 domains seized and 23 servers taken down across seven countries; U.S. officials froze about $3.5 million in cryptocurrency.
- FBI: AVRecon targets approximately 1,200 device models from Cisco, D-Link, Hikvision, MicroTik, Netgear, TP-Link, and Zyxel.
- Court documents linked SocksEscort infrastructure to scams including fraudulent unemployment claims, cryptocurrency theft, and U.S. bank account takeovers; operators allegedly earned more than $5.7 million (Europol cited ~$5.8 million received).
- Black Lotus Labs: The platform averaged ~20,000 distinct victims weekly and routed communications through an average of 15 C2 nodes; impact peaked in January 2025 at more than 15,000 victims daily.
Next Steps
- Inventory and patch internet-facing routers/IoT devices.
- Hunt for AVRecon indicators on edge devices.
Read more at Recorded Future News (The Record), The Hacker News, BleepingComputer, SecurityWeek, CyberScoop, Hackread
Subscribe
Subscribe to receive this weekly cybersecurity news summary to your inbox every Monday.


